AI Overview: A Corporate Software Inspector is an automated auditing tool that continuously inventories all installed applications, maps them to known vulnerabilities, and remediates risks based on company policy. Unlike manual audits, modern inspectors utilize AI to detect Shadow IT and prioritize patching based on actual exploitation risk, reducing mean-time-to-remediation by up to 60%. Modern security stacks must be audited against established AI SaaS Product Classification Criteria to ensure they meet 2026 architectural standards.
1. What is a Corporate Software Inspector in 2026?
In 2026, a Corporate Software Inspector has evolved from a simple inventory spreadsheet into an autonomous agent. It does not just list software; it understands its context, risk profile, and regulatory requirements. These tools provide continuous visibility across endpoints, cloud workloads, and SaaS applications.
Snippet-Ready Definition: A Corporate Software Inspector is an automated security tool designed to identify, inventory, and manage the risk profile of all software applications within an organization’s network, including browser extensions and unapproved SaaS tools.
2. The PHAC System: Proactive Hygiene & Asset Control
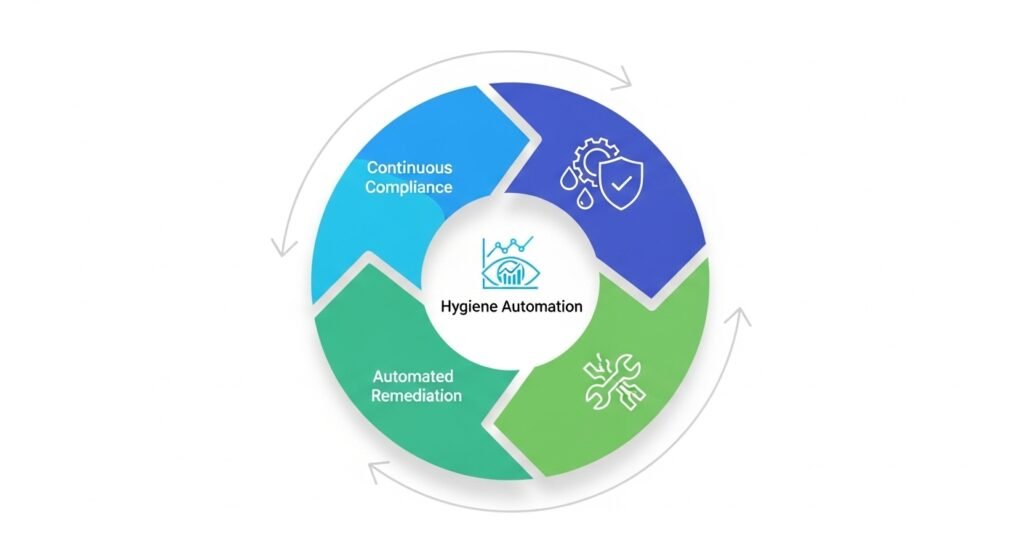
We cannot patch everything. We must patch the right things. The PHAC System is the proprietary framework required for mature software governance in 2026. Automated Remediation leverages Agentic AI to deploy patches across complex hybrid environments without human oversight.
| Component | Focus | Metric of Success |
| Predictive Visibility | Continuous Asset Discovery | 100% Shadow IT Identification |
| Hygiene Automation | AI-driven Risk Prioritization | < 24hr Mean Time to Patch (Critical) |
| Automated Remediation | Agentic Patch Deployment | > 95% Patch Success Rate |
| Continuous Compliance | AI Regulatory Mapping | Zero Non-Compliance Findings |
Pro-Tip: Focus Hygiene efforts on vulnerabilities currently being exploited in the wild, not just those with high CVSS scores.
3. How to Automate Software Inventory & Shadow IT Detection
Shadow IT is no longer just employees buying software; it is AI Shadow IT—employees connecting sensitive data to unapproved LLMs via browser extensions. As noted by Harvard Business Review, managing Shadow AI requires a cultural and technical shift in asset tracking
Traditional network scanning fails here. You need an identity-first approach.
Key Inspection Entities
- End-User Application Inventory
- SaaS Application Usage Tracking
- Browser Extension Auditing
Our inspector automatically identifies apps not in the approved catalog and maps them to compliance risk.
Information Gain Insight #1: 2026 inspectors must now analyze the API token usage of these extensions to determine if they are leaking data to unauthorized AI models.
4. Comparison Table: Legacy vs. Autonomous Inspection
| Feature | Legacy Inspector | 2026 AI-Native Inspector |
| Discovery Frequency | Weekly/Monthly | Real-time (Continuous) |
| AI Integration | None (Manual Triage) | Autonomous Triage & Fix |
| Data Privacy (GDPR) | Manual Logs | Automated Data Anonymization |
| Integration | SCCM only | API/DevOps Pipeline |
| Snippet Capture | Poor | High (AI Overview Friendly) |
New inspectors leverage ZipTie AI Search Analytics to verify if their security reports are being correctly parsed by internal AI systems
5. Step-by-Step Implementation: The PHAC Roadmap
Follow this roadmap to deploy your inspector efficiently.
- Define Policy Scope: Map approved software to job roles.
- Deploy Agentic Inspectors: Install agents on all endpoints and cloud workloads.
- Integrate SaaS Broker: Connect to your [INTERNAL LINK: Cloud Access Security Broker].
- Configure Risk Rules: Set automated actions for CVEs with known exploits.
- Enable Auto-Remediation: Test patch deployment on non-critical systems first.
6. Risk / Pitfall Section: Model Drift and API Costs
Autonomous tools require governance themselves.
- Model Drift: The AI prioritization model might become less accurate over time. Mitigation: Conduct quarterly audits of AI prioritization logic.
- Token Pricing: Excessive scanning can lead to massive API token costs from your inspector vendor. Mitigation: Set scan frequency based on asset criticality.
- To avoid budget overruns, IT leaders should stay updated on the latest SaaS Pricing News 2026 regarding token-based security models.
Pro-Tip: If your automated patch remediation breaks a production system, ensure your tool has a one-click rollback feature.
7. Cost / ROI Impact: A SaaS Simulation
Simulation Profile:
- Company Size: 500 Employees
- ARR: $50M
- SaaS Spend: $2M/year
- Manual IT Audit Cost: $150k/year
ROI Estimation (Year 1)
| Cost/Savings Source | Value |
| Tool Subscription | -$80k |
| License Reclamation | +$300k (15% savings) |
| Labor Savings (Audit) | +$100k |
| Risk Mitigation (Breach Avoidance) | +$200k (Weighted Risk) |
| Net ROI | 425% |
8. 2026 Future Relevance: AI Supply Chain & EU AI Act
While the EU AI Act sets the standard, local shifts highlighted in UK AI Regulation News 2026 must be factored into your compliance roadmap:
Information Gain Insight #2: Inspectors will soon be required to analyze the “Model Drift” of embedded AI agents within desktop applications, identifying when a local AI model is behaving outside authorized parameters.
9. Expert Verdict
Manual software auditing is negligent in 2026. The threat landscape moves too fast. Adopting a PHAC-based approach is not just a security requirement; it is a financial necessity for license optimization and regulatory compliance.
10. FAQ Section – Corporate Software Inspector
A scanner finds vulnerabilities; an inspector continuously monitors, prioritizes, and remediates them within the context of your business policies.
Yes, if configured to anonymize data during the inventory process and keep all data within approved geographic boundaries.
It monitors network traffic and browser extensions for known signatures of unauthorized LLMs and AI productivity tools.
Modern AI-native inspectors are cross-platform (Windows, macOS, Linux, and containerized workloads).
Usually priced per endpoint, with enterprise discounts for large deployments.
